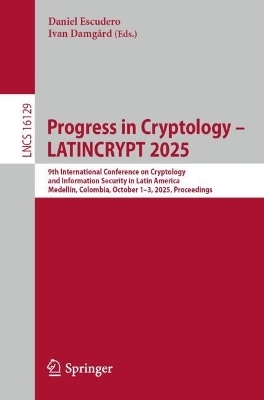
Progress in Cryptology – LATINCRYPT 2025
Springer International Publishing (Verlag)
978-3-032-06753-1 (ISBN)
This book constitutes the refereed proceedings of the 9th International Conference on Cryptology and Information Security in Latin America, LATINCRYPT 2025, held in Medellín, Colombia, in October 2025.
The 17 full papers included in this book were carefully reviewed and selected from 41 submissions.They were focused on the following topical sections: Position Paper; Zero-Knowledge Proofs and Distributed Computation; Quantum and Post-Quantum Cryptography; Symmetric-Key Cryptography and Attacks; Machine Learning and Cryptanalysis; and Implementation and Efficiency.
.- Position Paper.
.- Cryptography and Collective Power.
.- Zero-Knowledge Proofs and Distributed Computation.
.- Post-Quantum Zero-Knowledge with Space-Bounded Simulation.
.- Adaptive UC NIZK for Practical Applications.
.- Fast elliptic curve scalar multiplications in SN(T)ARK circuits.
.- Great-LaKeys: An Improved Threshold-PRF and a Novel Exponent-VRF from LWR.
.- Quantum and Post-Quantum Cryptography.
.- Orient Express: Using Frobenius to Express Oriented Isogenies.
.- Improved algorithms for ascending isogeny volcanoes, and applications.
.- The Tate Profile.
.- Extending Regev s quantum algorithm to elliptic curves.
.- The role of piracy in quantum proofs.
.- Symmetric-Key Cryptography and Attacks.
.- (Im)Possibility of Symmetric Encryption against Coordinated Algorithm Substitution Attacks and Key Exfiltration.
.- A Simple Forgery Attack on Pelican.
.- From at Least $n/3$ to at Most $3sqrt{n}$: Correcting the Algebraic Immunity of the Hidden Weight Bit Function.
.- Machine Learning and Cryptanalysis.
.- Generic Partial Decryption as Feature Engineering for Neural Distinguishers.
.- Extracting Some Hidden Layers of Deep Neural Networks in the Hard-Label Setting.
.- Implementation and Efficiency.
.- Rhizomes and the Roots of Efficiency Improving Prio.
.- Runtime Code Generation for Constant-Time Secret-Indexed Array Accesses: Applications to PERK and NTRU.
| Erscheinungsdatum | 06.10.2025 |
|---|---|
| Reihe/Serie | Lecture Notes in Computer Science |
| Zusatzinfo | XII, 489 p. 64 illus., 19 illus. in color. |
| Verlagsort | Cham |
| Sprache | englisch |
| Maße | 155 x 235 mm |
| Themenwelt | Informatik ► Theorie / Studium ► Kryptologie |
| Schlagworte | Cryptanalysis • cryptographic protocols • Elliptic Curve Cryptography • isogeny-based cryptography • post-quantum cryptography • Public-Key Cryptography • Quantum Cryptography • Secure Multiparty Computation • symmetric cryptography • Zero-knowledge proofs |
| ISBN-10 | 3-032-06753-7 / 3032067537 |
| ISBN-13 | 978-3-032-06753-1 / 9783032067531 |
| Zustand | Neuware |
| Informationen gemäß Produktsicherheitsverordnung (GPSR) | |
| Haben Sie eine Frage zum Produkt? |
aus dem Bereich